448 search results - page 32 / 90 » Active Matching |
103
click to vote
CHI
1997
ACM
15 years 6 months ago
1997
ACM
An ecological-cognitive framework of analysis and a model-tracing architecture are presented and used in the analysis of data recorded from users browsing a large document collect...
111
click to vote
SIGMOD
2001
ACM
16 years 2 months ago
2001
ACM
Intrusion detection systems have traditionally been based on the characterization of an attack and the tracking of the activity on the system to see if it matches that characteriz...
112
click to vote
NIPS
1997
15 years 3 months ago
1997
Most computational engineering based loosely on biology uses continuous variables to represent neural activity. Yet most neurons communicate with action potentials. The engineerin...
125
click to vote
ICIP
2003
IEEE
16 years 4 months ago
2003
IEEE
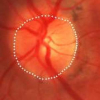
This paper presents efficient methods for automatic detection and extraction of blood vessels and optic disc (OD) both of which are two prominent anatomical structures in ocular f...
124
Voted
FGCN
2008
IEEE
15 years 8 months ago
2008
IEEE
When recording extracellular neural activity, it is often necessary to distinguish action potentials arising from distinct cells near the electrode tip, a process commonly referre...