577 search results - page 51 / 116 » An enterprise assurance framework |
ACSAC
2001
IEEE
14 years 1 months ago
2001
IEEE
The Java Cryptography Architecture, JCA in short, was created to allow JCA-compliant cryptography providers to be plugged into a JCA-aware application at run time. This configurab...
FITRAMEN
2008
13 years 11 months ago
2008
This paper proposes a study of the IPTV world, focusing on network and system architectures, video codecs, network protocols, services and quality assurance. Based on this study, a...
ICIP
2005
IEEE
14 years 11 months ago
2005
IEEE
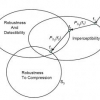
We introduce a set theoretic framework for watermarking and illustrate its effectiveness by designing a hierarchical semi-fragile watermark that is tolerant to compression and all...
COMPSAC
2006
IEEE
14 years 4 months ago
2006
IEEE
Web applications have become complex and crucial in many fields. In order to assure their quality, a high demand for systematic methodologies of Web application testing is emergin...
TOIT
2010
13 years 8 months ago
2010
The increasing demand for high-bandwidth applications such as video-on-demand and grid computing is reviving interest in bandwidth reservation schemes. Earlier attempts did not ca...