3628 search results - page 657 / 726 » Approaching the Physical Limits of Computing |
266
click to vote
VLDB
2007
ACM
16 years 4 months ago
2007
ACM
Whenever an intrusion occurs, the security and value of a computer system is compromised. Network-based attacks make it difficult for legitimate users to access various network ser...
157
click to vote
CVPR
2010
IEEE
16 years 25 days ago
2010
IEEE
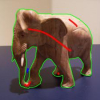
Interactive segmentation is useful for selecting objects of interest in images and continues to be a topic of much study. Methods that grow regions from foreground/background seed...
125
click to vote
WWW
2010
ACM
15 years 11 months ago
2010
ACM
Semantic Web data exhibits very skewed frequency distributions among terms. Efficient large-scale distributed reasoning methods should maintain load-balance in the face of such hi...
111
click to vote
CHI
2010
ACM
15 years 11 months ago
2010
ACM
Many tasks require attention switching. For example, searching for information on one sheet of paper and then entering this information onto another one. With paper we see that pe...
120
click to vote
CVPR
2007
IEEE
15 years 10 months ago
2007
IEEE
Registering consecutive images from an airborne sensor into a mosaic is an essential tool for image analysts. Strictly local methods tend to accumulate errors, resulting in distor...