286 search results - page 55 / 58 » Authentication in the Taos Operating System |
146
Voted
JAVA
2001
Springer
15 years 8 months ago
2001
Springer
CX, a network-based computational exchange, is presented. The system’s design integrates variations of ideas from other researchers, such as work stealing, non-blocking tasks, e...
177
Voted
NSPW
1998
ACM
15 years 7 months ago
1998
ACM
Object-based programming is becoming more and more popular and is currently conquering the world of distributed programming models. In object-based systems access control is often...
117
Voted
COMPSEC
2010
15 years 2 months ago
2010
Making backup is so cumbersome and expensive that individuals hardly ever backup their data and companies usually duplicate their data into a secondary server. This paper proposes...
136
Voted
LCN
2000
IEEE
15 years 8 months ago
2000
IEEE
Virtual private networks (VPNs) allow two or more parties to communicate securely over a public network. Using cryptographic algorithms and protocols, VPNs provide security servic...
126
Voted
ICPR
2006
IEEE
16 years 4 months ago
2006
IEEE
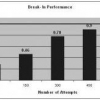
Regeneration of biometric templates from match scores has security and privacy implications related to any biometric based authentication system. In this paper, we propose a novel...