1150 search results - page 19 / 230 » Beacon Based Authentication |
113
click to vote
COMSWARE
2006
IEEE
15 years 8 months ago
2006
IEEE
Abstract— In this paper, we propose an authentication and secure channel establishment protocol that is reliable and adaptable for multihop wireless home networks. The main idea ...
132
click to vote
ICPPW
2009
IEEE
15 years 9 months ago
2009
IEEE
—Pervasive computing is fast becoming a reality with rapid advance in computing and networking technologies. It has the characteristics of scalability, invisibility, and the abse...
167
click to vote
EUC
2008
Springer
15 years 4 months ago
2008
Springer
Password authentication is a popular approach used for user authentication in pervasive computing environments due to its simplicity and convenience. To secure the transmission be...
111
click to vote
ICIP
2006
IEEE
16 years 4 months ago
2006
IEEE
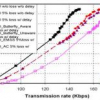
Stream authentication methods usually impose overhead and dependency among packets. The straightforward application of state-of-the-art rate-distortion (R-D) optimized streaming t...
120
click to vote
ICSNC
2007
IEEE
15 years 8 months ago
2007
IEEE
- The number of different identities and credentials used for authentication towards services on the Internet has increased beyond the manageable. Still, the most common authentica...