2877 search results - page 188 / 576 » Computational Biology |
143
click to vote
TEC
2002
15 years 4 months ago
2002
With increased global interconnectivity, reliance on e-commerce, network services, and Internet communication, computer security has become a necessity. Organizations must protect ...
109
click to vote
ISBI
2004
IEEE
16 years 5 months ago
2004
IEEE
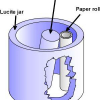
We have recently proposed and investigated a planar imaging method called multiple-image radiography (MIR) that concurrently produces three two-dimensional images that reveal info...
166
click to vote
SIGMOD
2004
ACM
16 years 4 months ago
2004
ACM
The detection of correlations between different features in a set of feature vectors is a very important data mining task because correlation indicates a dependency between the fe...
148
Voted
IJCNN
2006
IEEE
15 years 10 months ago
2006
IEEE
— Neuronal morphology plays a crucial role in the information processing capabilities of neurons. Despite the importance of morphology for neural functionality, biological data i...
141
click to vote
ISAAC
2005
Springer
15 years 10 months ago
2005
Springer
Consider two phylogenetic networks N and N′ of size n. The tripartition-based distance finds the proportion of tripartitions which are not shared by N and N′ . This distance i...