24529 search results - page 37 / 4906 » Computing on Authenticated Data |
134
click to vote
IJNSEC
2007
15 years 2 months ago
2007
A protocol for secure communication between set-top box and smart card in conditional access system is proposed. The proposed protocol uses the Schnorr identification scheme to a...
110
Voted
ICIP
2006
IEEE
16 years 4 months ago
2006
IEEE
Stream authentication methods usually impose overhead and dependency among packets. The straightforward application of state-of-the-art rate-distortion (R-D) optimized streaming t...
153
click to vote
PERCOM
2009
ACM
15 years 9 months ago
2009
ACM
—Privacy protection is increasingly important during authentications in Radio Frequency Identification (RFID) systems. In order to achieve high-speed authentication in largescale...
111
click to vote
ICC
2007
IEEE
15 years 8 months ago
2007
IEEE
- In the paper, we propose an efficient two-factor localized authentication scheme suitable for WLAN roaming. The proposed authentication scheme can greatly improve the security co...
158
click to vote
WMASH
2003
ACM
15 years 7 months ago
2003
ACM
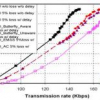
A serious challenge for seamless roaming between independent wireless LANs (WLANs) is how best to confederate the various WLAN service providers, each having different trust relat...