3374 search results - page 551 / 675 » Explaining Similarity of Terms |
164
click to vote
EUROSYS
2008
ACM
16 years 3 months ago
2008
ACM
Eudaemon is a technique that aims to blur the borders between protected and unprotected applications, and brings together honeypot technology and end-user intrusion detection and ...
204
click to vote
ALT
2008
Springer
16 years 2 months ago
2008
Springer
Abstract For many centuries scientists have wondered how the human brain represents thoughts in terms of the underlying biology of neural activity. Philosophers, linguists, cogniti...
138
click to vote
CSCW
2010
ACM
16 years 2 months ago
2010
ACM
In recent years, a growing number of studies examining how culture shapes computer-mediated communication (CMC) have appeared in the CHI and CSCW literature. Findings from these s...
182
click to vote
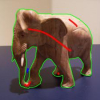
CVPR
2010
IEEE
16 years 2 months ago
2010
IEEE
Interactive segmentation is useful for selecting objects of interest in images and continues to be a topic of much study. Methods that grow regions from foreground/background seed...
166
click to vote
WWW
2010
ACM
16 years 26 days ago
2010
ACM
User experience in social media involves rich interactions with the media content and other participants in the community. In order to support such communities, it is important to...