853 search results - page 7 / 171 » Flexible authentication of images |
ISCAS
2005
IEEE
14 years 1 months ago
2005
IEEE
—The pervasive distribution of digital images triggers an emergent need of authenticating degraded images by lossy compression and transmission. This paper proposes a robust cont...
PCM
2009
Springer
14 years 1 days ago
2009
Springer
Abstract. In this paper, we propose an image moment-based geometric normalization to be applied before embedding and extracting a digital watermark in the DWT-domain of JPEG2000. A...
ICIP
2009
IEEE
13 years 5 months ago
2009
IEEE
ICIP
2006
IEEE
14 years 9 months ago
2006
IEEE
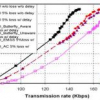
Stream authentication methods usually impose overhead and dependency among packets. The straightforward application of state-of-the-art rate-distortion (R-D) optimized streaming t...
ICIP
2006
IEEE
14 years 9 months ago
2006
IEEE
Digital images have been used in growing number of applications from law enforcement and surveillance, to medical diagnosis and consumer photography. With such widespread populari...