822 search results - page 8 / 165 » Hashing Methods for Temporal Data |
151
click to vote
CVPR
2012
IEEE
13 years 4 months ago
2012
IEEE
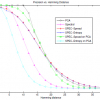
Many binary code encoding schemes based on hashing have been actively studied recently, since they can provide efficient similarity search, especially nearest neighbor search, an...
ISI
2007
Springer
15 years 8 months ago
2007
Springer
—A digital chain of custody is an account documenting digital data at a particular place and time. This paper gives a method of validating and authenticating a digital chain of c...
160
click to vote
ESWS
2009
Springer
15 years 5 days ago
2009
Springer
Many applications operate on time-sensitive data. Some of these data are only valid for certain intervals (e.g., job-assignments, versions of software code), others describe tempor...
134
click to vote
ALENEX
2009
15 years 3 months ago
2009
Minimal perfect hash functions have been shown to be useful to compress data in several data management tasks. In particular, order-preserving minimal perfect hash functions [10] ...
143
Voted
CVPR
2010
IEEE
15 years 10 months ago
2010
IEEE
Searching approximate nearest neighbors in large scale high dimensional data set has been a challenging problem. This paper presents a novel and fast algorithm for learning binary...