1254 search results - page 62 / 251 » Making Hard Problems Harder |
147
click to vote
SIGMOD
2011
ACM
14 years 5 months ago
2011
ACM
Complex social and information network search becomes important with a variety of applications. In the core of these applications, lies a common and critical problem: Given a labe...
115
click to vote
SIGSOFT
2007
ACM
16 years 3 months ago
2007
ACM
Asynchronous systems components are hard to write, hard to reason about, and (not coincidentally) hard to mechanically verify. In order to achieve high performance, asynchronous c...
116
click to vote
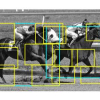
CVPR
2008
IEEE
16 years 4 months ago
2008
IEEE
This paper describes a discriminatively trained, multiscale, deformable part model for object detection. Our system achieves a two-fold improvement in average precision over the b...
110
click to vote
ICDCS
2009
IEEE
15 years 12 months ago
2009
IEEE
Peer-to-peer file sharing is popular, but it generates random write traffic to storage due to the nature of swarming. NAND flash memory based Solid-State Drive (SSD) technology...
122
click to vote
ACSC
2006
IEEE
15 years 9 months ago
2006
IEEE
Code obfuscation is a relatively new technique of software protection and it works by deterring reverse engineering attempts by malicious users of software. The objective of obfus...