54 search results - page 3 / 11 » Mining configurable enterprise information systems |
144
click to vote
SIGCOMM
2010
ACM
15 years 5 months ago
2010
ACM
Energy efficiency is becoming increasingly important in the operation of networking infrastructure, especially in enterprise and data center networks. While strategies for lowerin...
180
click to vote
AEI
2007
15 years 5 months ago
2007
Process mining techniques allow for extracting information from event logs. For example, the audit trails of a workflow management system or the transaction logs of an enterprise ...
150
click to vote
CCS
2009
ACM
16 years 14 days ago
2009
ACM
Role mining algorithms address an important access control problem: configuring a role-based access control system. Given a direct assignment of users to permissions, role mining...
150
click to vote
CSCWD
2005
Springer
15 years 7 months ago
2005
Springer
Process mining techniques allow for extracting information from event logs. For example, the audit trails of a workflow management system or the transaction logs of an enterprise ...
272
click to vote
SIGMOD
2008
ACM
17 years 4 months ago
2008
ACM
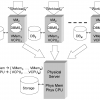
Virtual machine monitors are becoming popular tools for the deployment of database management systems and other enterprise software applications. In this paper, we consider a commo...