2272 search results - page 293 / 455 » Provable Data Privacy |
112
click to vote
COCOON
2010
Springer
15 years 7 months ago
2010
Springer
We study algorithms for clustering data that were recently proposed by Balcan, Blum and Gupta in SODA’09 [4] and that have already given rise to two follow-up papers. The input f...
264
click to vote
ICDE
2009
IEEE
17 years 2 months ago
2009
IEEE
Existing approaches on privacy-preserving data publishing rely on the assumption that data can be divided into quasi-identifier attributes (QI) and sensitive attribute (SA). This ...
108
click to vote
MHCI
2009
Springer
15 years 9 months ago
2009
Springer
With SeCuUI we present a solution that aims to increase security of data entry on public terminals. The user can enter all data requested by the terminal using her mobile device. ...
151
Voted
BTW
2005
Springer
15 years 8 months ago
2005
Springer
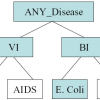
: Access control is an important aspect in guaranteeing data privacy within XML data sources which are accessed by users with different access rights. The goal of predicative acces...
131
click to vote
OOPSLA
2004
Springer
15 years 8 months ago
2004
Springer
Component-based enterprise systems often suffer from performance issues as a result of poor system design. In this paper, we propose a framework to automatically detect, assess an...