316 search results - page 54 / 64 » Radon-Based Structure from Motion without Correspondences |
162
click to vote
ICITA
2005
IEEE
15 years 11 months ago
2005
IEEE
Intrusion Detection Systems (IDS) have become widely used tools for ensuring system and network security. Among many other challenges, contemporary IDS have to cope with increasin...
147
click to vote
FSS
2006
15 years 5 months ago
2006
Among the various extensions to the common [0, 1]-valued truth degrees of "traditional" fuzzy set theory, closed intervals of [0, 1] stand out as a particularly appealin...
137
click to vote
BMCBI
2005
15 years 5 months ago
2005
Background: In a previous report (La et al., Proteins, 2005), we have demonstrated that the identification of phylogenetic motifs, protein sequence fragments conserving the overal...
166
click to vote
ECCV
2006
Springer
16 years 7 months ago
2006
Springer
Triangulation consists in finding a 3D point reprojecting the best as possible onto corresponding image points. It is classical to minimize the reprojection error, which, in the p...
164
click to vote
CVPR
2005
IEEE
16 years 7 months ago
2005
IEEE
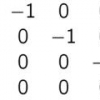
Matrix factorization has many applications in computer vision. Singular Value Decomposition (SVD) is the standard algorithm for factorization. When there are outliers and missing ...