3605 search results - page 701 / 721 » Securing Security Policies in Autonomic Computing Systems |
144
click to vote
ANCS
2006
ACM
15 years 11 months ago
2006
ACM
The fast spreading worm is becoming one of the most serious threats to today’s networked information systems. A fast spreading worm could infect hundreds of thousands of hosts w...
142
click to vote
MSWIM
2005
ACM
15 years 10 months ago
2005
ACM
Wireless sensor networks (WSNs) have many potential applications. Furthermore, in many scenarios WSNs are of interest to adversaries and they become susceptible to some types of a...
161
click to vote
ANCS
2007
ACM
15 years 9 months ago
2007
ACM
There is a growing interest in designing high-performance network devices to perform packet processing at flow level. Applications such as stateful access control, deep inspection...
167
click to vote
DEBS
2007
ACM
15 years 6 months ago
2007
ACM
This paper describes an approach to detect unknown event patterns. In this context, an event is not only something that happens, but also something that can be analysed. This task...
141
click to vote
ICPR
2006
IEEE
16 years 6 months ago
2006
IEEE
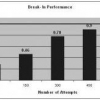
Regeneration of biometric templates from match scores has security and privacy implications related to any biometric based authentication system. In this paper, we propose a novel...