434 search results - page 49 / 87 » The Case for Browser Provenance |
165
click to vote
CCS
2011
ACM
14 years 5 months ago
2011
ACM
Search engine optimization (SEO) techniques are often abused to promote websites among search results. This is a practice known as blackhat SEO. In this paper we tackle a newly em...
185
click to vote
INFOCOM
2009
IEEE
16 years 15 days ago
2009
IEEE
—A major problem in wireless networks is coping with limited resources, such as bandwidth and energy. These issues become a major algorithmic challenge in view of the dynamic nat...
145
click to vote
POLICY
2007
Springer
15 years 12 months ago
2007
Springer
The implementation of network security devices such as firewalls and IDSs are constantly being improved to accommodate higher security and performance standards. Using reliable a...
165
click to vote
CVPR
2009
IEEE
17 years 1 months ago
2009
IEEE
Many perception and multimedia indexing problems involve datasets that are naturally comprised of multiple streams or modalities for which supervised training data is only sparsely...
153
click to vote
IPMI
2003
Springer
16 years 6 months ago
2003
Springer
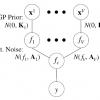
The Gaussian distribution is the basis for many methods used in the statistical analysis of shape. One such method is principal component analysis, which has proven to be a powerfu...