525 search results - page 60 / 105 » A Fair e-Tendering Protocol |
163
click to vote
CORR
2006
Springer
15 years 5 months ago
2006
Springer
Broadcasting is known to be an efficient means of disseminating data in wireless communication environments (such as Satellite, mobile phone networks,...). It has been recently ob...
158
click to vote
TCC
2009
Springer
16 years 6 months ago
2009
Springer
It is well known that general secure function evaluation (SFE) with information-theoretical (IT) security is infeasible in presence of a corrupted majority in the standard model. ...
201
click to vote
TON
2010
15 years 16 days ago
2010
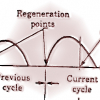
Abstract--Every congestion control protocol operating in wireless networks is potentially faced with two major challenges of performance degradation. These sources are (a) the coup...
156
click to vote
FOCS
2006
IEEE
15 years 12 months ago
2006
IEEE
Secret sharing and multiparty computation (also called “secure function evaluation”) are fundamental primitives in modern cryptography, allowing a group of mutually distrustfu...
281
click to vote
Publication
We propose a scheme for congestion avoidance in networks using a connectionless protocol at the network layer. The scheme uses a minimal amount of feedback from the network to the ...