9611 search results - page 108 / 1923 » A Note on Difference Sets |
133
click to vote
ETS
2002
IEEE
15 years 2 months ago
2002
IEEE
In this paper we briefly discuss the knowledge-on-demand (KOD) paradigm as it emerges from the current needs of the knowledge-based society. Basic requirements for on-demand learn...
120
click to vote
SICHERHEIT
2010
15 years 1 months ago
2010
We introduce a new representation for monitored behavior of malicious software called Malware Instruction Set (MIST). The representation is optimized for effective and efficient a...
146
click to vote
BMCBI
2007
15 years 3 months ago
2007
Background: Gene Set Enrichment Analysis (GSEA) is a computational method for the statistical evaluation of sorted lists of genes or proteins. Originally GSEA was developed for in...
145
click to vote
ARC
2008
Springer
15 years 5 months ago
2008
Springer
Over the last years, we have witnessed the increased use of Application-Specific Instruction-Set Processors (ASIPs). These ASIPs are processors that have a customizable instruction...
238
click to vote
Publication
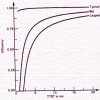
The performance of Fiber-Distributed Data Interface (FDDI) depends upon several workload parameters; for example; the arrival pattern, frame size, and configuration parameters, suc...