314 search results - page 38 / 63 » Concurrently Decomposable Constraint Systems |
166
click to vote
SENSYS
2010
ACM
15 years 2 months ago
2010
ACM
Wireless sensor networks (WSNs) are hard to program due to unconventional programming models used to satisfy stringent resource constraints. The common event-driven concurrent pro...
169
click to vote
IEEECIT
2010
IEEE
15 years 1 months ago
2010
IEEE
Future systems will have to support multiple and concurrent dynamic compute-intensive applications, while respecting real-time and energy consumption constraints. With the increase...
134
click to vote
ECCV
2000
Springer
16 years 6 months ago
2000
Springer
In this paper, we address the problem of visually guiding and controlling a robot in projective three-space using stereo vision. As the proposed method is entirely formulated in pr...
129
click to vote
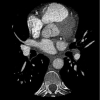
ISBI
2008
IEEE
16 years 5 months ago
2008
IEEE
Multi-detector Computed Tomography offers the promise of a non-invasive alternative to invasive coronary angiography for the evaluation of coronary artery disease. An impediment p...
146
click to vote
CCS
2010
ACM
15 years 4 months ago
2010
ACM
Attackers often take advantage of vulnerabilities in benign software, and the authors of benign software must search their code for bugs in hopes of finding vulnerabilities before...