221 search results - page 41 / 45 » Data Hiding Techniques Using Prime and Natural Numbers |
137
click to vote
WWW
2004
ACM
16 years 5 months ago
2004
ACM
It is increasingly common for users to interact with the web using a number of different aliases. This trend is a doubleedged sword. On one hand, it is a fundamental building bloc...
136
click to vote
CRYPTO
2005
Springer
15 years 10 months ago
2005
Springer
Broadcast encryption schemes allow a message sender to broadcast an encrypted data so that only legitimate receivers decrypt it. Because of the intrinsic nature of one-to-many comm...
131
click to vote
SIGSOFT
2009
ACM
16 years 5 months ago
2009
ACM
Software engineering researchers have long been interested in where and why bugs occur in code, and in predicting where they might turn up next. Historical bug-occurence data has ...
144
click to vote
VIS
2005
IEEE
16 years 5 months ago
2005
IEEE
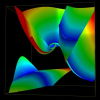
Tensor topology is useful in providing a simplified and yet detailed representation of a tensor field. Recently the field of 3D tensor topology is advanced by the discovery that d...
256
click to vote
POPL
2009
ACM
16 years 5 months ago
2009
ACM
Self-adjusting computation is an evaluation model in which programs can respond efficiently to small changes to their input data by using a change-propagation mechanism that updat...