717 search results - page 139 / 144 » Dynamic Link Measurements Using Active Components |
144
click to vote
SYSTOR
2009
ACM
15 years 11 months ago
2009
ACM
A typical storage hierarchy comprises of components with varying performance and cost characteristics, providing multiple options for data placement. We propose and evaluate a hie...
177
click to vote
TES
2001
Springer
15 years 9 months ago
2001
Springer
Current developments show that tomorrow’s information systems and applications will no longer be based on monolithic architectures that encompass all the functionality. Rather, t...
227
click to vote
BIRTHDAY
2011
Springer
14 years 4 months ago
2011
Springer
Abstract. Risk analysis has been used to manage the security of systems for several decades. However, its use has been limited to offline risk computation and manual response. In c...
139
click to vote
ICCV
1999
IEEE
16 years 6 months ago
1999
IEEE
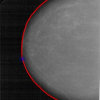
Since their debut in 1987, snakes (active contour models) have become a standard image analysis technique with several variants now in common use. We present a framework called ``...
137
click to vote
EXPCS
2007
15 years 8 months ago
2007
Predictors are inherent components of state-of-the-art microprocessors. Branch predictors are discussed actively from diverse perspectives. Performance of a branch predictor large...