1660 search results - page 94 / 332 » Forwarding in a content-based network |
162
click to vote
WINET
2010
15 years 2 months ago
2010
Wireless sensor networks comprise typically dense deployments of large networks of small wireless capable sensor devices. In such networks, multicast is a fundamental routing servi...
138
click to vote
PERCOM
2005
ACM
16 years 4 months ago
2005
ACM
The biggest challenge for RFID technology is to provide benefits without threatening the privacy of consumers. Many solutions have been suggested but almost as many ways have been...
111
click to vote
EUROPKI
2004
Springer
15 years 9 months ago
2004
Springer
The security-mediated approach to PKI offers several advantages, such as instant revocation and compatibility with standard RSA tools. In this paper, we present a design and protot...
254
click to vote
Publication
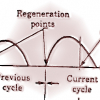
We propose a scheme for congestion avoidance in networks using a connectionless protocol at the network layer. The scheme uses a minimal amount of feedback from the network to the ...
117
click to vote
GCC
2003
Springer
15 years 9 months ago
2003
Springer
Peer-to-peer networking is a hot buzzword that has been sweeping through the computing industry over the past year or so. Gnutella, as one of the first operational pure P2P systems...