151 search results - page 20 / 31 » Minimality Attack in Privacy Preserving Data Publishing |
SDM
2009
SIAM
14 years 4 months ago
2009
SIAM
In this paper, we study the problem of how to generate synthetic graphs matching various properties of a real social network with two applications, privacy preserving social netwo...
VLDB
2007
ACM
14 years 8 months ago
2007
ACM
Recent research studied the problem of publishing microdata without revealing sensitive information, leading to the privacy preserving paradigms of k-anonymity and -diversity. k-a...
CCS
2009
ACM
14 years 2 months ago
2009
ACM
Genome-wide association studies (GWAS) aim at discovering the association between genetic variations, particularly single-nucleotide polymorphism (SNP), and common diseases, which...
TCC
2005
Springer
14 years 1 months ago
2005
Springer
Abstract. We initiate a theoretical study of the census problem. Informally, in a census individual respondents give private information to a trusted party (the census bureau), who...
ICDE
2009
IEEE
15 years 7 months ago
2009
IEEE
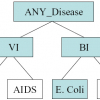
Existing approaches on privacy-preserving data publishing rely on the assumption that data can be divided into quasi-identifier attributes (QI) and sensitive attribute (SA). This ...