2612 search results - page 328 / 523 » Mobile Processes and Termination |
125
click to vote
ISBI
2006
IEEE
16 years 5 months ago
2006
IEEE
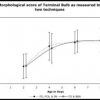
We are studying the genetic influence on rates of age related muscle degeneration in C. elegans. For this, we built pattern recognition tools to calculate a morphological score gi...
126
click to vote
KDD
2002
ACM
16 years 5 months ago
2002
ACM
Security of computer systems is essential to their acceptance and utility. Computer security analysts use intrusion detection systems to assist them in maintaining computer system...
131
click to vote
STOC
2001
ACM
16 years 5 months ago
2001
ACM
This article introduces and explores the condition-based approach to solve the consensus problem in asynchronous systems. The approach studies conditions that identify sets of inpu...
143
click to vote
MOBIHOC
2001
ACM
16 years 4 months ago
2001
ACM
The development of practical, localized algorithms is probably the most needed and most challenging task in wireless ad-hoc sensor networks (WASNs). Localized algorithms are a spe...
143
click to vote
DSD
2009
IEEE
15 years 11 months ago
2009
IEEE
—Long test application time and high temperature have become two major issues of system-on-chip (SoC) test. In order to minimize test application times and avoid overheating duri...