5476 search results - page 987 / 1096 » Resettably Secure Computation |
163
click to vote
CCGRID
2003
IEEE
15 years 9 months ago
2003
IEEE
The availability of digital imagers inside hospitals and their ever growing inspection capabilities have established digital medical images as a key component of many pathologies ...
127
click to vote
NSDI
2004
15 years 5 months ago
2004
Over the past few years, a relatively new computing phenomenon has gained momentum: the spread of "spyware." Though most people are aware of spyware, the research commun...
316
click to vote
ICDE
2008
IEEE
17 years 4 months ago
2008
IEEE
Existing work on privacy-preserving data publishing cannot satisfactorily prevent an adversary with background knowledge from learning important sensitive information. The main cha...
301
click to vote
Book
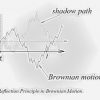
This is a great draft book about stochastic calculus and finance. It covers large number of topics such as Introduction to Probability Theory, Conditional Expectation, Arbitrage Pr...
110
click to vote
ICML
2009
IEEE
16 years 5 months ago
2009
IEEE
Conventional clustering methods typically assume that each data item belongs to a single cluster. This assumption does not hold in general. In order to overcome this limitation, w...