128 search results - page 25 / 26 » Verifying Process Algebra Proofs in Type Theory |
137
Voted
CSFW
2002
IEEE
15 years 8 months ago
2002
IEEE
We describe a protocol design process, and illustrate its use by creating ATSPECT, an Authentication Test-based Secure Protocol for Electronic Commerce Transactions. The design pr...
140
click to vote
VIS
2005
IEEE
16 years 5 months ago
2005
IEEE
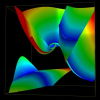
Tensor topology is useful in providing a simplified and yet detailed representation of a tensor field. Recently the field of 3D tensor topology is advanced by the discovery that d...
223
click to vote
POPL
2005
ACM
16 years 4 months ago
2005
ACM
A lightweight logical approach to race-free sharing of heap storage between concurrent threads is described, based on the notion of permission to access. Transfer of permission be...
153
Voted
TOPLAS
2008
15 years 3 months ago
2008
act Interpretation C. BERNARDESCHI, N. DE FRANCESCO, G. LETTIERI, L. MARTINI, and P. MASCI Universit`a di Pisa Bytecode verification is a key point in the security chain of the Jav...
249
Voted
POPL
2007
ACM
16 years 4 months ago
2007
ACM
This paper proposes a lightweight fusion method for general recursive function definitions. Compared with existing proposals, our method has several significant practical features...