420 search results - page 7 / 84 » Isosurface Computation Made Simple |
109
click to vote
BMCBI
2010
15 years 3 months ago
2010
Background: The binding of peptide fragments of antigens to class II MHC is a crucial step in initiating a helper T cell immune response. The identification of such peptide epitop...
147
click to vote
SGP
2007
15 years 5 months ago
2007
We introduce an algorithm for reconstructing watertight surfaces from unoriented point sets. Using the Voronoi diagram of the input point set, we deduce a tensor field whose princ...
121
click to vote
TASLP
2010
15 years 1 months ago
2010
Abstract—We present an algorithm for removing timefrequency components, found by a standard Gabor transform, of a “real-world” sound while causing no audible difference to th...
128
click to vote
CORR
1999
Springer
15 years 2 months ago
1999
Springer
Quantum key distribution is the best known application of quantum cryptography. Previously proposed proofs of security of quantum key distribution contain various technical subtle...
161
click to vote
VIS
2004
IEEE
16 years 4 months ago
2004
IEEE
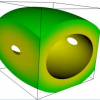
We describe a general algorithm to produce compatible 3D triangulations from spatial decompositions. Such triangulations match edges and faces across spatial cell boundaries, solv...