521 search results - page 98 / 105 » Mining Mobility Behavior from Trajectory Data |
166
click to vote
MDM
2009
Springer
16 years 12 days ago
2009
Springer
Mobile Ad-hoc NETworks (MANETs) are known to be vulnerable to a variety of attacks due to lack of central authority or fixed network infrastructure. Many security schemes have bee...
179
click to vote
RTCSA
2007
IEEE
16 years 3 days ago
2007
IEEE
This work is motivated by a strong market demand in the replacement of NOR flash memory with NAND flash memory to cut down the cost in many embedded-system designs, such as mobi...
162
click to vote
VIS
2005
IEEE
16 years 7 months ago
2005
IEEE
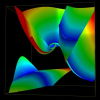
Tensor topology is useful in providing a simplified and yet detailed representation of a tensor field. Recently the field of 3D tensor topology is advanced by the discovery that d...
199
click to vote
SIGSOFT
2010
ACM
15 years 3 months ago
2010
ACM
The transfer of entire projects to offshore locations, the aging and renewal of core developers in legacy products, the recruiting in fast growing Internet companies, and the part...
201
click to vote
HUC
2011
Springer
14 years 5 months ago
2011
Springer
Sensor-enabled smartphones are opening a new frontier in the development of mobile sensing applications. The recognition of human activities and context from sensor-data using cla...