2212 search results - page 357 / 443 » Weighted control scheduling |
141
Voted
ESORICS
2010
Springer
15 years 4 months ago
2010
Springer
Abstract. We introduce a novel remotely-mounted attack that can expose the network identity of an anonymous client, hidden service, and anonymizing proxies. To achieve this, we emp...
174
Voted
JSAC
2008
15 years 3 months ago
2008
We propose the cross-layer based opportunistic multi-channel medium access control (MAC) protocols, which integrate the spectrum sensing at physical (PHY) layer with the packet sch...
151
Voted
JFR
2007
15 years 3 months ago
2007
To achieve the ever increasing demand for science return, planetary exploration rovers require more autonomy to successfully perform their missions. Indeed, the communication dela...
152
click to vote
CVPR
2010
IEEE
15 years 12 months ago
2010
IEEE
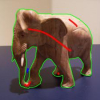
Interactive segmentation is useful for selecting objects of interest in images and continues to be a topic of much study. Methods that grow regions from foreground/background seed...
143
click to vote
ICIP
2008
IEEE
15 years 10 months ago
2008
IEEE
This appendix proves the illumination robustness of the proposed corner detector over the Harris corner detector. I. HARRIS CORNER DETECTOR The Harris corner detector [1] is based...